Meta Description: Need to securely connect to your remote servers, home lab, or office network? This guide compares self-hosted VPNs, mesh VPNs, and tunneling tools to help you choose the right approach.
Introduction
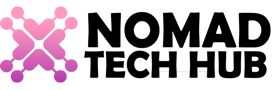
You’ve got a server in a datacenter, a home lab running in your garage, and an office network with resources you need to access remotely. Maybe you’re a sysadmin managing infrastructure, a homelab enthusiast tinkering with self-hosted services, or a developer who needs access to staging environments from anywhere.
The question isn’t whether you need a VPN — it’s which type of VPN you need.
Traditional consumer VPNs (NordVPN, ExpressVPN, etc.) route your internet traffic through a remote server to hide your IP and encrypt your browsing. That’s not what we’re talking about here. This guide is about infrastructure VPN tools — the kind you use to securely connect servers, home labs, and office networks together.
There are three main approaches today, each with its own strengths:
- Self-Hosted VPN — WireGuard or OpenVPN running on your own server
- Mesh VPN — Tailscale, Netbird, Netmaker, or Twingate
- Reverse Tunnel — Cloudflare Tunnel or frp
This guide breaks down each approach so you can pick the right one for your setup.
The Core Approaches
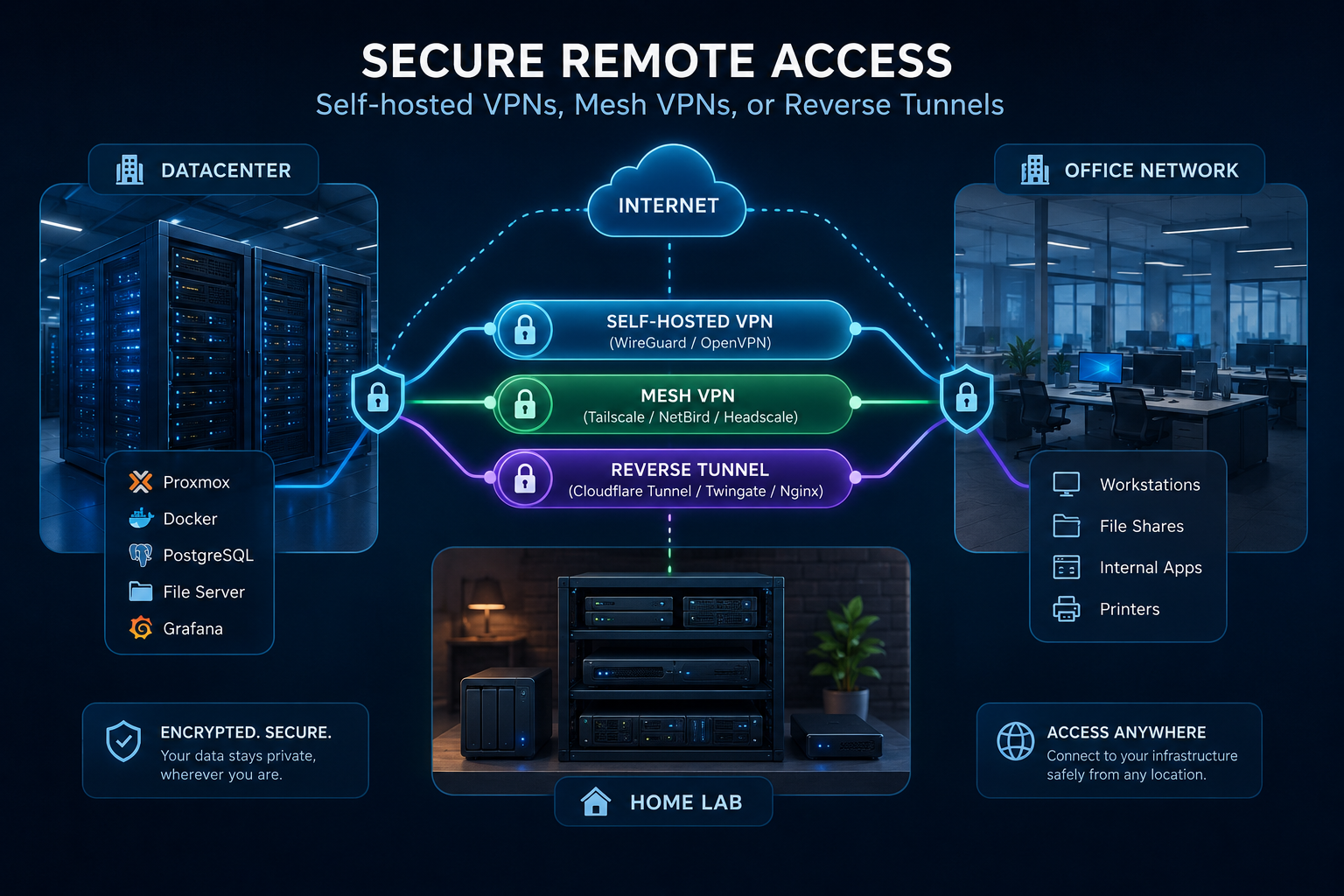
Self-Hosted VPN (WireGuard / OpenVPN)
This is the classic approach. You set up a VPN server on a VPS or at your office, and your devices (laptops, phones, other servers) connect to it as clients. All traffic between your devices and your private network flows through an encrypted tunnel.
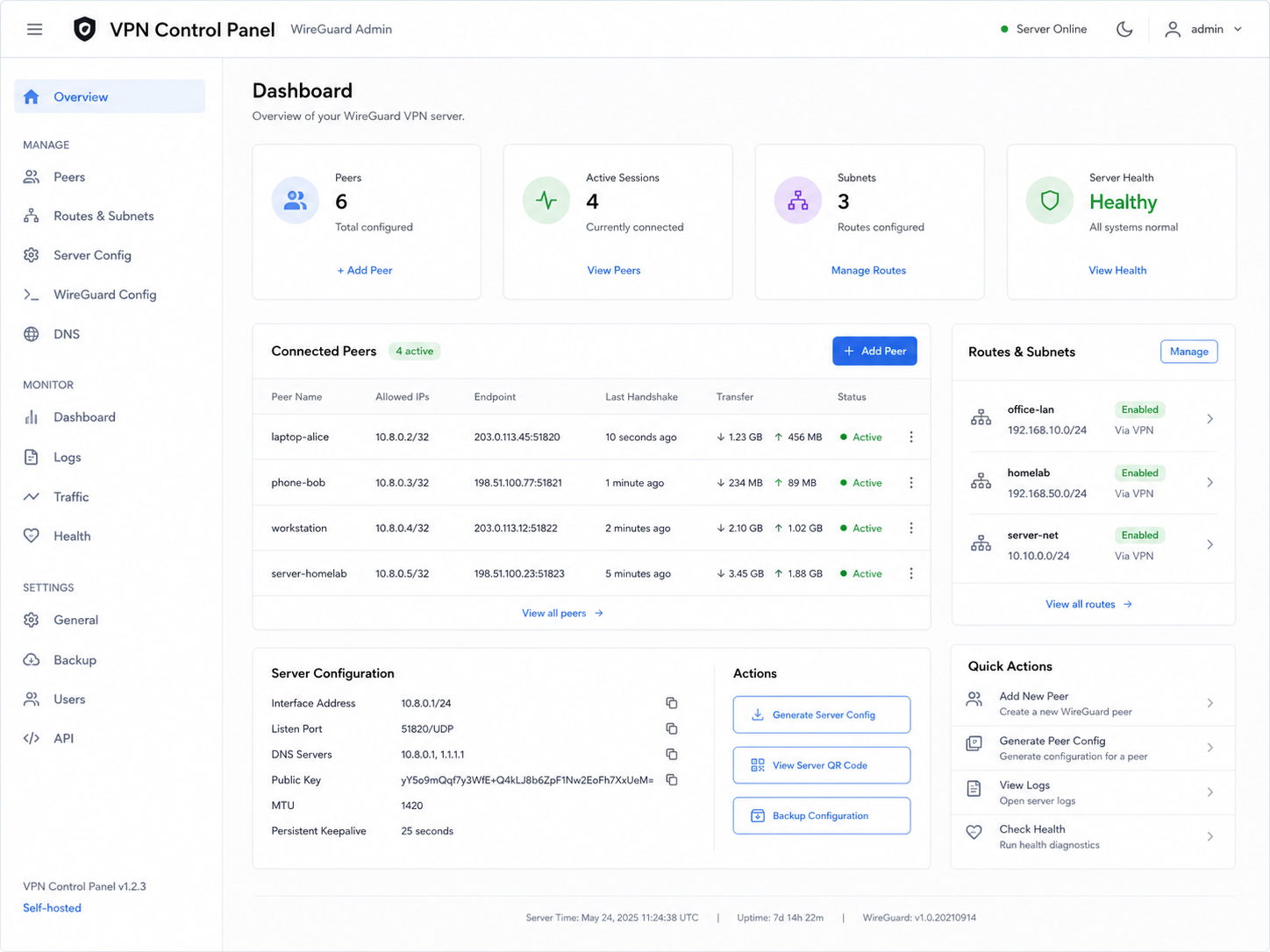
WireGuard is the modern standard — it’s part of the Linux kernel, incredibly fast, and minimal by design. A complete WireGuard setup is often just a few config files and a single wg-quick up command.
OpenVPN is older but more feature-rich — it supports TCP fallback, obfuscation, and more complex authentication setups. It’s slower than WireGuard but battle-tested over decades.
Best for:
- Site-to-site VPNs (connecting whole networks together)
- Full network access to your home lab or office
- When you want complete control over the infrastructure
- Technical users comfortable managing a server
Trade-offs:
- You manage the server — updates, monitoring, uptime
- Requires a public-facing VPS or port forwarding on your router
- Adding/removing clients means updating configs
Typical stack: WireGuard on a $5-10 VPS + wg-quick on each client.
Mesh VPN (Tailscale / Netbird / Netmaker / Twingate)
Mesh VPNs are the modern evolution. Instead of a hub-and-spoke model (one server, many clients), every device in your network connects directly to every other device — peer-to-peer. They handle NAT traversal automatically using technologies like STUN, TURN, and ICE, so you don’t need to open ports or configure a central server.
Tailscale — Built on WireGuard. The easiest to set up, with a generous free tier (up to 3 users, 100 devices). Uses your existing identity provider (Google, GitHub, Microsoft) for authentication. Installs in minutes.
Netbird — Open source mesh VPN with built-in access controls. Free tier includes up to 10 users, 100 devices. Self-hostable if you want full control.
Netmaker — More advanced. Lets you create a full WireGuard mesh network with a central controller. Supports both mesh and hub-and-spoke topologies. Self-hosted only.
Twingate — Zero Trust Network Access (ZTNA) approach. Instead of giving devices access to your whole network, you define specific resources (SSH on one server, RDP on another) and grant granular access. More enterprise-oriented.
Best for:
- Connecting multiple remote servers, laptops, and phones
- Teams that need simple, secure access to infrastructure
- When you don’t want to manage a VPN server
- Dynamic environments where devices come and go
Trade-offs:
- You rely on a coordination server (except with self-hosted Netbird/Netmaker)
- Less control over the underlying network configuration
- Free tiers have limits on users/devices
Reverse Tunnel (Cloudflare Tunnel / frp / ngrok)
These tools don’t create a traditional VPN network. Instead, they create an outbound tunnel from your server to a public edge, and you access your services through that edge. No open ports, no public IP required.
Cloudflare Tunnel — Runs a cloudflared daemon on your server that connects to Cloudflare’s edge network. You access your services through your domain via Cloudflare’s proxy. Supports built-in authentication (cloudflared access) for an extra security layer.
frp (fast reverse proxy) — Self-hosted reverse tunnel. You run a server on a public VPS and clients connect to it. Supports TCP, UDP, HTTP, and HTTPS tunnels.
ngrok — Commercial tunneling service. Generates public URLs for local servers. Useful for development and demos rather than permanent infrastructure.
Best for:
- Exposing self-hosted services without opening firewall ports
- Development and testing (webhooks, API testing)
- When you can’t configure port forwarding on your network
- Sharing access to specific services rather than whole networks
Trade-offs:
- Service-level access only — not full network connectivity
- Latency through the edge network
- Bandwidth limits on free tiers
- Cloudflare Tunnel requires a domain managed by Cloudflare
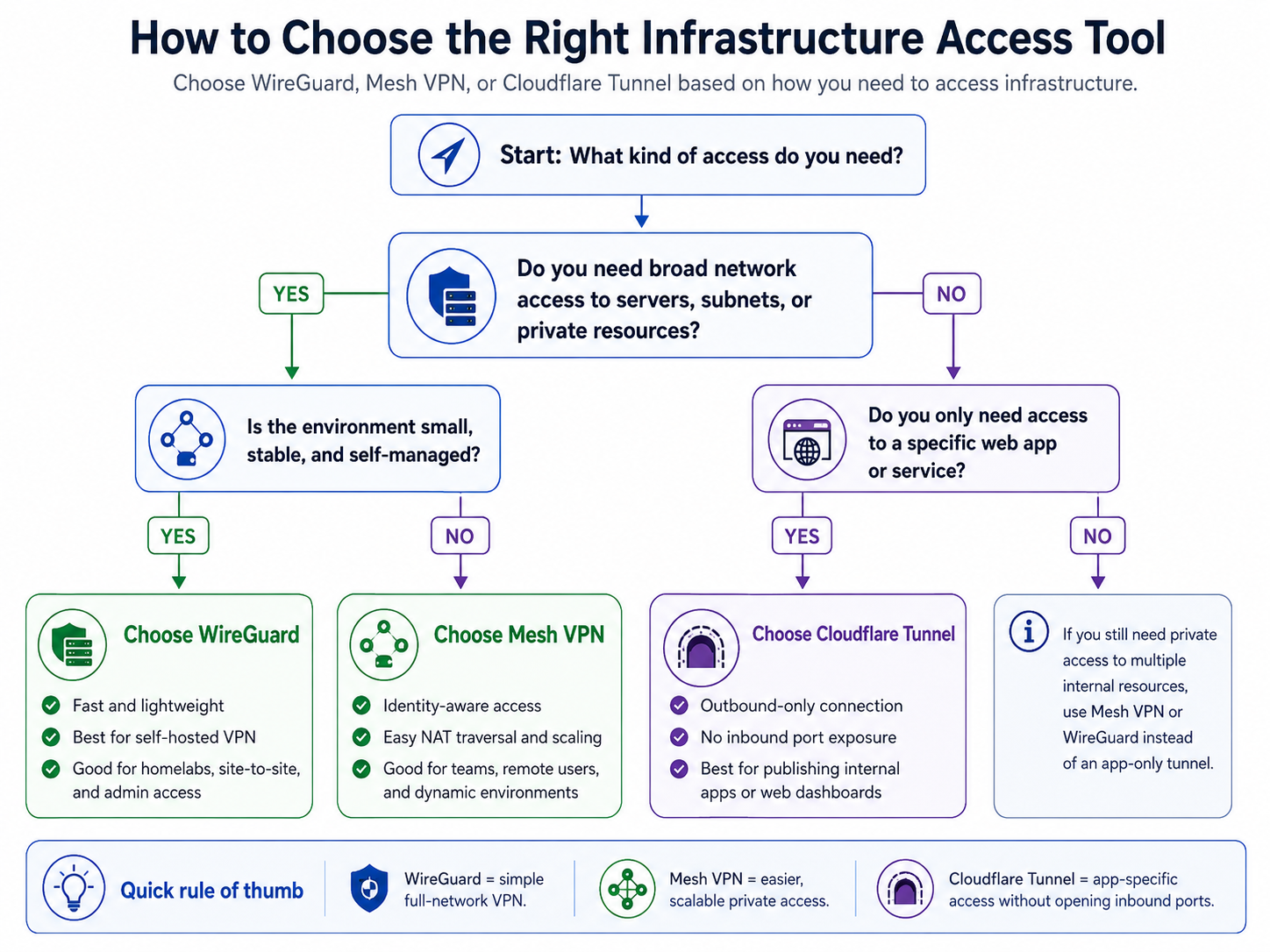
Decision Framework
Choose Self-Hosted VPN (WireGuard) if:
- You need full network access — not just individual services
- You want to connect entire networks together (site-to-site)
- You’re comfortable managing a Linux server
- You need maximum performance with minimum overhead
- You want zero dependency on third-party services
→ Start with: WireGuard on a $5 VPS — it’s simple, fast, and you own the whole stack.
Choose Mesh VPN if:
- You have many devices (10+) across different locations
- You want something that “just works” out of the box
- You need to connect laptops, phones, and servers together
- You don’t want to manage a central VPN server
- You’re working in a team and need simple onboarding
→ Start with: Tailscale — easiest setup, generous free tier, works everywhere.
→ If you want open source: Netbird — self-hostable or cloud, similar functionality.
→ If you need granular access control: Twingate — zero trust, resource-level permissions.
Choose Reverse Tunnel if:
- You want to expose a web app, API, or service without opening ports
- You can’t configure port forwarding on your network
- You need a quick solution for development or testing
- You want Cloudflare’s DDoS protection and CDN in front of your services
→ Start with: Cloudflare Tunnel — free, reliable, integrates with Cloudflare’s ecosystem.
→ If you want self-hosted: frp — full control, but more setup.
Quick Comparison
| Feature | Self-Hosted VPN | Mesh VPN | Reverse Tunnel |
|---|---|---|---|
| Setup complexity | Medium-High | Low | Low-Medium |
| Server management | You manage it | None (or optional) | Minimal |
| Network access | Full network | Full network | Service only |
| NAT traversal | Requires open ports | Automatic (NAT traversal) | Outbound only |
| Performance | Best (direct) | Good (sometimes relayed) | Depends on edge |
| Best for | Site-to-site, power users | Multi-device, teams | Exposing services |
| Cost | VPS ($3-10/mo) | Free tier available | Free tier available |
Putting It All Together
Here’s how the decision flows in practice:
Scenario 1: I have a home lab and want to access it from my laptop anywhere
Self-hosted WireGuard on a Raspberry Pi or low-power server at home. Port forward on your router or use a VPS as a relay. Simple, reliable, full network access.
Or skip the port forwarding: Use Tailscale. Install it on your home server and laptop. Done. The mesh handles NAT traversal automatically.
Scenario 2: I manage multiple servers across different providers
Tailscale or Netbird. Install the agent on each server, and they can all talk to each other securely over encrypted peer-to-peer connections. No need to configure firewall rules for each pair.
Scenario 3: I want to share a web app running on my home server with a client
Cloudflare Tunnel. Run cloudflared tunnel on the server, point your domain at it, and your client accesses it through Cloudflare. No open ports, HTTPS enforced, DDoS protection included.
Scenario 4: I need access to my office network from remote employee laptops
WireGuard site-to-site VPN or a mesh VPN like Tailscale/Twingate. For granular access control (SSH access to specific servers only), Twingate’s zero trust model shines.
Common Mistakes
- Using a consumer VPN for server access — NordVPN, ExpressVPN, and similar services won’t help you connect to your home lab. They’re designed for privacy, not infrastructure.
- Not planning for growth — A simple WireGuard config for 3 devices is easy. Scaling it to 30 devices without automation tools (or switching to a mesh VPN) is painful.
- Opening too many ports — If your home lab needs 10 open ports to be useful, you’re doing it wrong. Tunnel or mesh VPN approaches eliminate the need for exposed ports entirely.
- Ignoring NAT traversal — Your office network might have a strict firewall that blocks incoming connections. Mesh VPNs handle this automatically; self-hosted setups require careful planning.
- Overlooking key rotation — WireGuard keys are long-lived by default. Mesh VPNs typically handle key rotation automatically. If you’re self-hosting, set a reminder to rotate keys periodically.
Key Takeaways
- Infrastructure VPN tools serve a fundamentally different purpose from consumer privacy VPNs — don’t confuse the two
- WireGuard is the backbone protocol, but how you deploy it (self-hosted vs mesh vs tunnel) depends on your use case
- Mesh VPNs (Tailscale, Netbird) are the easiest path for most users — they handle the hard parts automatically
- Cloudflare Tunnel is the best option for exposing services without opening ports
- The right choice depends on: number of devices, network topology, team size, and your tolerance for server management
- You can also combine approaches — WireGuard for site-to-site + Cloudflare Tunnel for specific services
Related Content
- WireGuard vs OpenVPN — Deep technical comparison of the two self-hosted protocols
- Self-Host Your Own VPN — Step-by-step guide to deploying WireGuard on a $5 VPS
- Tailscale vs Twingate vs Netbird vs Netmaker — Mesh VPN comparison
- Cloudflare Tunnel vs VPN — When to tunnel vs when to VPN
- VPN for AI Agent Server — Securing access to your AI/agent infrastructure
Call to Action
Start with the simplest solution that meets your needs. If you have a handful of devices and don’t want to manage infrastructure, try Tailscale’s free tier. If you want full control, spin up WireGuard on a VPS. If you need to expose services, set up a Cloudflare Tunnel.
What’s your current setup for remote server and network access? Drop a comment or reach out — we’d love to hear what works for you.